Most cryptocurrencies since the introduction of Bitcoin have been designed to employ the proof of work consensus mechanism in order to prevent manipulation of financial records on their respective blockchains. The process requires cryptocurrency miners to compute a unique solution for a mathematical function, which is otherwise known as a cryptographic hash function. The computational effort undertaken by the miner is to ensure that all transactions within that block are legitimate.
Before addressing what cryptographic hash functions are in the context of cryptocurrencies though, it is in order to have a general understanding of the concept first. The term ‘hashing’ typically involves taking a sequence of characters and passing it through a mathematical function to get an output of some length.
Even small variations in the input, including interchanging an uppercase character for a lowercase one, will drastically change the output hash. Hashing is also a one-way operation, which means that there is no way to reverse the operation to get the input again, making it difficult for any human or computer to simply find the result.
Hash Functions in Bitcoin
In Bitcoin and most other cryptocurrencies, the input for the hash function comprises of transaction details along with timestamps and other relevant data. The length of the output hash is fixed as per the algorithm’s specifications. SHA-256, for instance, always outputs a hash with a length of 256-bits.
While hashing has only recently started to gain mainstream traction due to blockchain’s rise in the popularity, the process has actually already been in use for several other non-blockchain related applications as well. Website password storage is actually one of the most common applications of cryptographic hashing. In short, most modern websites perform the hashing process to prevent storing an exact copy of user password on their servers. This way, in the event of a security breach, attackers will simply get a copy of the password hashes, mitigating any damage done due to a full-blown data leak.
Like most mathematical processes, hash functions tend to vary quite widely in terms of complexity. A more complex hashing algorithm will typically make be much more stronger and difficult for a hacker to brute force into.
While using the most secure algorithm currently available may seem like the best course of action, it is important to note that the increased complexity often comes requires significantly more time and computational power. Considering that a large number of cryptocurrency enthusiasts already believe that specialized ASIC mining is negatively impacting decentralization, striking a balance between security and convenience is essential.
Bitcoin uses the cryptographic hash function SHA-256, which is an acronym for Secure Hash Algorithm 256-bit. The algorithm was initially designed by the United States National Security Agency (NSA) with no intention for it to be used for cryptocurrencies whatsoever. The security benefits of this freely available mathematical process, however, made it a perfect fit for the Bitcoin network.
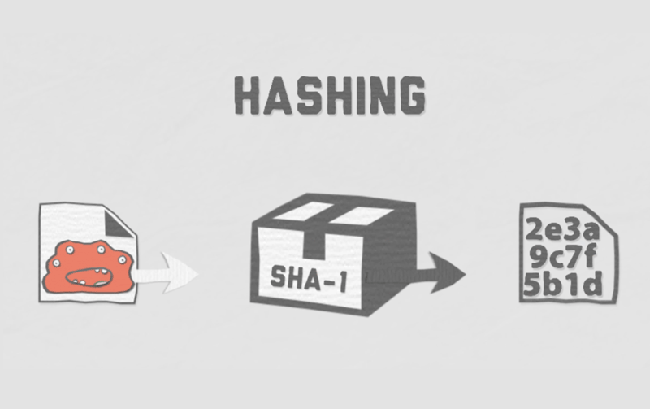
Image credits:
The SHA-256 hashing function is actually one of the most complicated cryptographic algorithms currently in use by digital currencies. Of course, competitors employing a simpler algorithm does not necessarily make them less secure in any way though. The added complexity is likely the reason why bitcoin has managed to stick around for almost a decade now and is still arguably the most trusted cryptocurrency on the market.
SHA-256 being complex in nature does not, however, make it difficult to understand and implement in hardware than other hashing algorithms. At its core, performing hashing using the function involves nothing more than simple boolean algebra and 32-bit addition, two tasks that computing devices have become exceedingly efficient at doing. The steps are so simple, in fact, that any ordinary human being could potentially do it as well, albeit several quintillion times slower than modern mining hardware.
It is because of this straightforward nature of the SHA-256 algorithm that custom-made mining chips (called ASICs) could be created for bitcoin. An ASIC, or application-specific integrated circuit, is basically a dedicated piece of hardware that typically consists of hundreds upon hundreds of such chips connected in parallel, all performing the singular task of successfully hashing the next bitcoin block.
Considering how specific the workload of an ASIC miner is then, it should come across as no surprise that they can easily output significantly more hashes than any consumer grade central processing unit (CPU) or graphics processing unit (GPU).
As previously mentioned though, not all cryptocurrencies are designed to use the SHA-256 hashing algorithm. Other cryptographic hash functions may even be less energy intensive due to their reduced complexity. Scrypt is perhaps the most well-known alternative and is in use by top currencies such as Litecoin and Dogecoin.
The Scrypt hash algorithm was released in 2009, the same year as bitcoin, and is generally preferred by new cryptocurrencies because it is faster and simpler than the tried and tested SHA-256.
Instead of relying on digital logic, it combines 1024 different hash values in a number of permutations to ultimately find a valid result. The downside to this approach is that storing so many values requires the algorithm to use a large amount of system memory, driving up the cost of hardware.
Scrypt, of course, is not the only other hash algorithm available and commonly in use. Other alternatives include X11, Cryptonight and Dagger Hashimoto, with one of them having their own unique characteristics.
While X11 has been tuned primarily for energy efficiency by requiring less wattage, Cryptonight is designed to be mined exclusively using desktop computer processors only. There is a long history of philosophical reasons that explains why these alternative algorithms have typically choose to prioritize a particular feature. In the case of Cryptonight, for instance, ASIC resistance was an important consideration while developing the algorithm, presumably to keep decentralization in the hands of a currency’s users.
Even though cryptographic hashing algorithms are designed to be able to resist attacks, there are a few attack vectors that can compromise an entire cryptocurrency network. For this reason, new hash functions are being continuously developed and researched by computer scientists and mathematicians. Modern algorithms can, after all, ensure increased collision, preimage and second preimage resistance, while still being efficient and practical enough for a cryptocurrency network.
Featured image