Just as Bitcoin is the original cryptocurrency, the Trezor is the original hardware wallet for storing your Bitcoins. The Trezor pioneered the hardware storage space for cryptocurrencies, and long enjoyed a large advantage over competitors in terms of security and features. While some competitors are arguably catching up to the Trezor, it is still one of the top choices for those who need a hardware storage solution for their Bitcoins and other alt-coins.
What Exactly is a Trezor?
The Trezor is a hardware cryptocurrency wallet that is used to store digital currencies such as Bitcoin safely offline. Basically it is a small computer whose function is to store the private keys associated with cryptocurrencies, and to digitally sign transactions when sending and receiving cryptocurrencies, without needing to be connected to the internet. It is an ideal way to store Bitcoins in a safe environment, but still have easy access to the Bitcoins.
In addition to the convenience of storing, sending and receiving digital currencies, you’ll also appreciate the small and compact size of the Trezor. The Trezor is pretty much no bigger than a potato chip, although it is bit thicker at 6mm or 0.2 inches thick. This means you can easily take it with you wherever you go, or it can be hidden in the smallest and most unexpected places. And when you’re ready to spend some Bitcoins you simply pull it out and connect it to a computer via USB and you’re ready to go.
Note that the USB connection used by the Trezor is a limited one, so it can send information over the computers internet connection, but there is no way for anyone to remotely access the Trezor while it is connected to the computer and the internet. Because there is no way to access the Trezor from the computer its connected to, you can even use a Trezor with a computer that has been infected with a virus or malware, and there’s no chance that your Bitcoins can be stolen. And once it is unplugged it is completely offline, keeping your Bitcoins safe and secure at all times.
Interesting note: The Trezor was developed by a Czech firm called SatoshiLabs. The word “Trezor” in Czech and most other Slavic languages translates to “Vault”, which is appropriate as the Trezor is a vault for your Bitcoins and other alt-coins.
Trezor Security Features
The Trezor lives up to its naming of “Vault” as it serves as a secure vault to store your Bitcoin holdings. In fact, in addition to Bitcoin, you can also store Litecoin, Dash, Zcash, Bitcoin Cash, Bitcoin Gold, Ethereum, Ethereum Classic, Expanse, UBIQ, NEM, Namecoin, Dogecoin and Bitcoin Testnet., and all of the ERC-20 coins that have been created. All of these coins can be stored safely and securely offline in your Trezor hardware wallet.
Let’s look at the security features that keep the Trezor so secure:
PIN Protection: When you first setup the Trezor you’ll have to create a PIN that is used to access the device later each time you use it. The Trezor team has create a unique method for keeping this PIN secure from hackers and keyloggers. The actual input of the PIN is done on an obscured keypad on your computer, but the numbers which correspond to each position on the keypad show on your Trezor screen, plus they are randomly scrambled. Here’s a photo to show exactly what I mean.
As you can see, there is no way that your entries can be discovered by a hacker, thief or any keylogging software.
Another feature of the PIN is that each time an incorrect PIN is entered to access the Trezor the time to enter the next PIN attempt increases exponentially. For example, after a nineteenth incorrect PIN entry you (or a thief) would have to wait 35 hours to make the twentieth PIN entry attempt. By the time you get to the twenty-ninth incorrect attempt the delay is 17 years to make the next attempt.
Physical Buttons: Each Trezor has physical buttons that need to be pressed to complete setup of the device, and later to confirm any transactions made. This means that even if your transaction is somehow compromised via a virus or malware, or some other form of hacking, it cannot be completed because the hacker will not be able to physically push these buttons to complete the transaction.
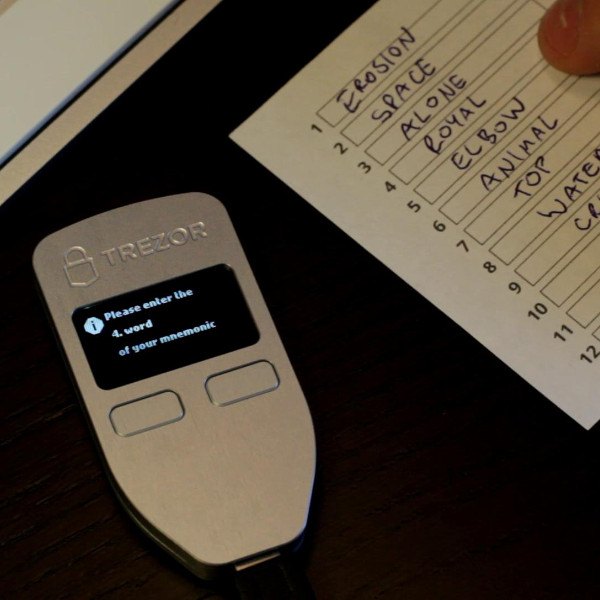
Trezor Recovery Phrase: The recovery phrase on the Trezor is a mnemonic code made of 12, 18 or 24 words depending on your choice. This seed is generated the first time you run TREZOR and will help you recovering its contents (private keys, bitcoin balance, and transaction history) into a new device if you ever lose or break your TREZOR, or if it is ever stolen. Without this recovery phrase no one can access your Bitcoins, even if they have physical possession of the Trezor device. And because the Trezor uses deterministic signatures and external random entropy sources, which means it uses multiple different sources to generate the ‘random’ seed, this phrase cannot be cracked by a standard random algorithm generator attack.
Trezor Passphrase Protection: For those who want even more security from a potential thief the Trezor supports the creation of a second “hidden” wallet using a second passphrase. This means you can store a small amount of Bitcoin in one wallet and the bulk of your Bitcoins in a second hidden wallet. If someone physically assaults you to get your passphrase you can then give them the first passphrase and they will make off with a small amount of Bitcoin, but your larger second wallet will remain hidden, safe and secure.
Using Your Trezor Hardware Wallet
The Trezor currently works with Windows (version 7 and higher), OSX (version 10.11 and higher), Linux and Android (with USB On-The-Go) operating systems. This means you can use it with nearly all desktop and laptop computers, and any mobile device or tablet running Windows 8.1 or Android.
The Trezor can be used with the included MyTrezor software wallet or the Trezor Chrome extension. Because these work on a single service, those wishing to avoid any type of centralization may opt for using a third party Bitcoin wallet instead. Currently the Trezor can be used in conjunction with a number of software and online client wallet services, including Mycellium and Electrum for software wallets. Note that the client wallets do not store any private keys, they simply display your balance and help manage transactions. You can find a complete list of supported client wallets here.
In addition to being a Bitcoin wallet, the Trezor has been developed to offer several other blockchain related services. While these are advanced features, they are all possible with the Trezor:
- Password Manager: Try out the next-generation password management app. Encrypt passwords separately and sync them to your private cloud, hassle-free, with TREZOR.
- Secure Admin SSH Access: Protect access to your servers, data or websites administration. SSH login with single or multiple sessions.
- 2-Factor Authentication: Safeguard your online accounts and identities. Enable the industry standard FIDO/U2F and use TREZOR as your security token.
- Sign & Encrypt with GPG: TREZOR encrypts every document or email you create with GPG.
- Password-less Login: Securely sign up and login with a click of a button, using TREZOR Connect.
- In the future developers will be able to create their own third-party apps for the Trezor, opening up a huge world of potential features and uses.
How is TREZOR different from…
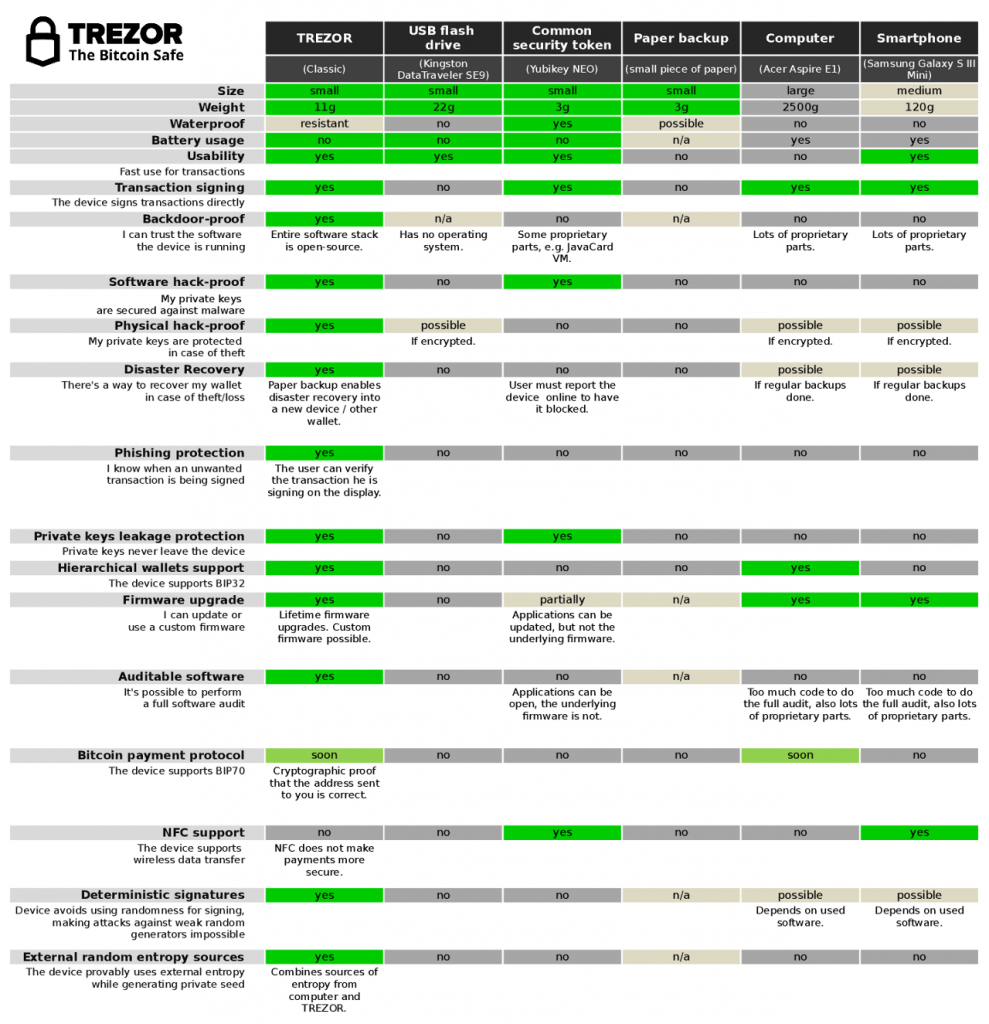
…a standard Web Wallet?
Using a standard web wallet puts your coins at risk of loss from several methods, including theft and even confiscation. Here’s a short list of ways in which people have lost coins in a web wallet over the years:
- User’s computer is hacked and web wallet password is stolen
- Web wallet server gets hacked and bitcoins are stolen
- Web wallet company goes bankrupt
- Law enforcement agency confiscates coins
- Web wallet provider points to ToS violation and takes coins
- Owners of web wallet company run away with coins
- Bug in web wallet software leads to loss of coins
- Your computer or cell phone is stolen while you are logged in and thieves then steal your coins
Keeping your Bitcoins in a TREZOR means none of these things can happen to you.
a desktop Bitcoin client?
While a desktop wallet is more secure than a web wallet, there is still the chance of being hacked and having your coins stolen. Malware and viruses can be introduced to your desktop computer, allowing bad actors to gain control of the desktop wallet and move all your coins out of your control.
your mobile phone?
Mobile phones are some of the least secure means of storing anything. And in most cases the mobile app used to transact is simply an interface to a web wallet that suffers the same security flaws. Others are little different from desktop wallets, and can be hacked or suffer malware attacks the same as the desktop.
a USB flash drive?
While a USB flash drive may seem safer at first glance, in reality it is simply storing your private keys offline, but when you want to make a transaction you’ll need to attach the flash drive to a computer, making it vulnerable to all of the hacks, malware and viruses that the computer is vulnerable to. At this point your USB flash drive is no different from a desktop wallet.
Trezor may remind you of a USB flash drive, but it is quite different in the way that it functions. Your Trezor device is a single-purpose computer and it can actively sign transactions without exposing your private keys to the computer it’s connected to. When you make a transaction with the Trezor the computer will send a transaction template to the Trezor, asking for a digital signature. You’ll see the transaction details right on the screen of the Trezor and can confirm the transaction (digitally signing it) at which point the Trezor sends the signed transaction back to the computer. This method never exposes your private keys to the computer or to the online world. This actually means you can process Bitcoin transactions with a Trezor even on a computer that has been infected with a virus and have no fears of losing your coins.
an encrypted wallet?
Encryption is a good security precaution, but it can’t stop a virus from sitting and waiting for you to transfer your coins, striking as soon as your private keys are exposed. There are also keylogger viruses that will record your keystrokes when you enter your passphrase for your wallet file, which negates the protection you get from encryption.
Again, the Trezor never sends your private keys to the computer it’s connected to. It simply gets the transaction file from the computer (think of it as an invoice being sent), signs the transaction, and then sends it back to the computer. There’s no time at which your private keys are made visible, and no way for anyone to send your coins away without your permission.
Yubikey?
A Yubikey is quite different from the Trezor. It helps verify that it is actually you signing a transaction, but it has no protections that would keep you from signing a transaction you hadn’t intended to sign.
a paper backup of my keys?
Paper backups are a secure offline solution, but if you want to send the Bitcoins to someone else you still need to enter your private keys onto a computer and hope it hasn’t been compromised in some way. Paper backups are also in danger of physical damage, such as water, fire or even being unintentionally thrown away.
In Conclusion
The Trezor is the original Bitcoin hardware wallet, and while competitors have made strides in catching up with them, it is still a very solid choice for those who want the security provided by a hardware wallet. My only disappointment with the Trezor was the choice to change from the original very solid metal version to a light-weight and less solid plastic model.
For a very reasonable price of just €89 or $99 you can’t do much better than the Trezor. If you do want to spend a bit less and still get a quality hardware wallet you may want to check out my Ledger Nano S review, but I still think the Trezor is the best on the market, and when they release the Trezor 2 I believe they will once again set the bar even higher.