Whether you’re a serious investor or simply a cryptocurrency enthusiast, you should know more about hardware wallets other than the fact that “they are used to store coins” — simply because that’s what a five-year-old child would say. So, in an effort to compile an easy-to-read overview of hardware wallets, we bring you this article.
We will start off by listing the different categories of cryptocurrency wallets, move on to hardware wallets and some of the building blocks that comprise them and, finally, compare three of the most popular alternatives: TREZOR, Ledger Nano S, and KeepKey. Hopefully, by the end of this article, you will have learned a couple of things about hardware wallets and educated yourself on the options you have should you decide to buy one. Let’s dive right in!
Cryptocurrency wallets 101
A crypto wallet is a kind of digital wallet that is used to send, receive and store cryptocurrency by means of public and private keys. The term itself is a bit ambiguous since we associate wallets with a place where actual coins are stored. This is not how cryptocurrency wallets work, though; the coins themselves aren’t stored anywhere and do not exist in physical form. Instead, they are represented by the transfer of their ownership i.e. by the transaction records written on the blockchain.
According to the platform, we differentiate between the following categories of cryptocurrency wallets:
Web wallets
Web wallets are accessible via web browser and rely on a trusted third party (like a crypto exchange) to maintain the safety and integrity of the user’s private keys. They do not require the user to spend time and storage space for downloading the full client software; they do, however, store the user’s wallet on a third party server which (as we’ve seen) can be compromised and result with the complete loss of the user’s funds. This tradeoff makes web wallets useful for storing smaller amounts of crypto that you transact with frequently, but it is inadvisable to rely on them (and their third-party servers) for storing large amounts of crypto.
Desktop wallets
Desktop wallets are installed on a desktop computer and store the user’s private keys on the computer’s hard drive. They are considered to be generally safer than online (web) wallets as they do not rely on external servers for the safekeeping of the user’s private keys. However, if the desktop computer in question is connected to the Internet, the desktop wallet is a form of hot storage which means it is inherently insecure. Desktop wallets offer more features and greater autonomy than web wallets do, but they are not the best alternative for long-term storage of your coins, especially large amounts that you don’t use very often.
Mobile wallets
Mobile wallets are an on-the-go alternative for active crypto enthusiasts that want to use their coins for micropayments on a daily basis. They offer all the basic necessary functionalities and are generally easy to use, which makes them suitable for beginners as well as power users. While indisputably convenient, the fact remains that mobile devices are more prone to theft than their desktop counterparts; therefore, mobile wallets should mostly be used for storing smaller amounts of crypto.
Paper wallets
Paper wallets are a form of cold storage, seeing as the wallet itself is nothing but a piece of paper (or metal, or wood) with the private and public keys written/engraved on it. In fact, it is the coldest of cold storage since, in order to take control of your coins, you need to manually type out your keys letter by letter. Obviously, paper wallets are amongst the safest of options for storing large amounts of crypto — as long as you don’t lose the piece of paper.
Hardware wallets
Hardware wallets are electronic devices that store the user’s private keys in a secure offline environment. This means that hardware wallets are virtually immune to hacking attacks and their biggest vulnerability is physical theft; even then, the device can be protected with a 4-8 digit PIN code that prevents the thief from accessing your private keys and you are able to restore the contents of your wallet using a recovery phrase. Let’s get the obvious question out of the way: why not just use a USB?
The answer is: a USB drive can only store your private keys; you’re still going to need a wallet (mobile/desktop/web…) to make the transaction. With hardware wallets the transaction signing happens inside the wallet, which means that your private keys are never transferred out of it and onto another type of wallet (mobile/desktop/web…), even though such website or software is used in the process.
You probably have other questions too but, before we get into how hardware wallets work and review some of the most popular options out there, we need to work our way through a couple of important concepts.
Let’s get familiar with BIPs (Bitcoin Improvement Proposals) – formal proposals that outline technical details for new features and changes that the author(s) wish to introduce to the Bitcoin network. Here are a couple of BIPs that are particularly important for hardware wallets:
- BIP32 (Hierarchical Deterministic Wallets) is a standard describing how you can build wallets in a tree structure that can be derived from a root key. Other (type 1) deterministic wallets generate new private key/public key pairs using the SHA-256 hashing algorithm; to generate a new key pair, the algorithm is provided with a seed (more on that later) and a random number n which starts from 1 and increments as additional keys are needed. Seeing as n is a random number, there is no way to recreate the private key that the algorithm SHA256(seed, n) was used to create and you would have to backup each wallet that was created in this manner individually. This is where type 2 (hierarchical deterministic) wallets come in. This type of wallet that was formally introduced in BIP32 enhances type 1 wallets with an organizational structure in which a private key (seed) can be thought of as being the root node of a tree structure, capable of reaching every other child-key below it. This concept is really useful in practice; imagine that you are the accountant of some company and you want to be able to allocate portions of the company’s budget to different departments. Hierarchical deterministic wallets allow for you to retain the control over the root private key and generate sub-wallets for different applications.
- BIP39 (Mnemonic code for generating deterministic keys) describes “the implementation of a mnemonic code or mnemonic sentence — a group of easy to remember words — for the generation of deterministic wallet.” In other words, BIP39 allows the creation of a mnemonic sentence and its conversion into a binary seed, which can be later used to generate a deterministic wallet using BIP32 or similar methods. The English language wordlist for the BIP39 standard is made up of 2048 words, making the number of 12-word seed phrases 2048 to the 12th power i.e. 2 to the 132nd power; this means that a 12-word phrase will have (somewhat less than) 132 bits of security. For 18-word seed phrases that number is about 198 bits, and for 24-word seed phrases it’s 264 bits of security. Note: the term “seed phrase/sentence” might be preferable over “mnemonic phrase/sentence” simply because the word “mnemonic” implies that the phrase should be memorized, which is inadvisable to say the least.
- BIP43 (Purpose Field for Deterministic Wallets) is another industry standard that introduces a “Purpose Field” to deterministic wallets. The reason for this is that the BIP32 specification is too broadly defined, allowing for different implementations of the proposal to exist. Some of those implementations may claim to be BIP32 compatible, but in fact aren’t; they produce wallets with different logical structures, making them essentially non-interoperable. BIP43 looks to evade this issue by proposing that the first level of the BIP32 structure be used as “purpose” which determines the further structure below that node.
- BIP44 (Multi-Account Hierarchy for Deterministic Wallets) is a particular implementation of BIP43 in that it defines a logical hierarchy for deterministic wallets based on BIP43’s purpose scheme. The hierarchy proposed in the paper allows the handling of multiple coins, multiple accounts, external and internal chains per account and millions of addresses per chain through the introduction of the following 5 levels in the BIP32 path: m / purpose’ / coin_type’ / account’ / change / address_index
Choosing a Hardware Wallet: Introduction to TREZOR, Ledger Nano S and KeepKey
Now that we’ve brushed up on our theory, let’s see how it translates into practice. In the following section we will look at the way the industry’s top 3 contenders protect your currency and allow you to transact with it — all that through the prism of three main safety mechanisms that most hardware wallets rely on: PIN numbers, recovery phrases and passphrases. We will also look at sending and receiving crypto using these devices, as well as review some of their physical and technical characteristics.
PIN number
To set up a hardware wallet, you connect it to your desktop or laptop via micro USB cable. The initial setup is relatively straightforward and can be done in a matter of minutes. The first prompt message that is displayed is – in regard to the device PIN code – a number that you enter as proof of ownership each time you want to use the device. Choose your PIN code, make sure you remember it, and never disclose it to anyone since knowing the PIN number of the hardware wallet lets you have complete control over it.
- Entering the wrong PIN three times in a row wipes Ledger Nano S wallets clean; this means that in order to be able to access your account again, you’ll have to enter your recovery phrase.
- With TREZOR, each time you enter a wrong PIN, the waiting time before you’re able to try again increases by a power of 2. The device wipes itself after 15 consecutive unsuccessful attempts.
- KeepKey allows for three regular attempts to enter the PIN, after which an automatic waiting period is imposed. The waiting period begins at 8 seconds, and increases exponentially with each subsequent failure (16, 32, 64, 128 seconds etc.).
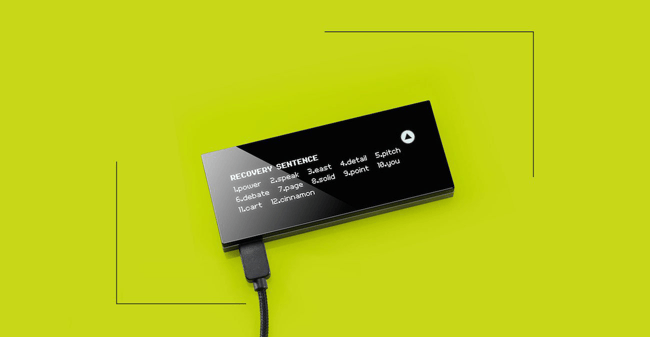
Recovery phrase
Once you’ve set up the PIN code, it’s time to write down the recovery phrase which will be displayed on your device’s screen. A BIP39 compliant hardware wallet allows for 12, 15, 18, 21 and 24-words-long recovery phrases. As the name suggests, the recovery phrase comes in handy when your hardware wallet gets damaged, misplaced or stolen; it allows the user to recover full access to their accounts with the use of any software or hardware wallet (including wallets from a different vendor) that supports the same standards as the original hardware wallet.
- A BIP32/39/44 compliant wallet for TREZOR and KeepKey
- A BIP39/44 compliant wallet for Ledger Nano S
You simply acquire a wallet that’s compliant with the same standards as your previous wallet and you enter the recovery words in the correct order. Needless to say, the recovery phrase is just as important as the PIN code in the context of the safety of your coins. Do not store it on a hot device (like your mobile phone or your computer) for obvious reasons; instead, write it on a piece of paper and put it in a safe place.
Passphrase
Many wallets support a recovery phrase two-factor authentication. If activated, the user will be given the regular 12/24 word recovery phrase and will be asked to provide an extra word that will act as a password (the terms “passphrase”, “13th/25th word”, “seed extension” and “extension word” are also used). The recovery process, then, will require the entering of 13/25 words total — the words from the recovery phrase + the password. It’s recommended that you don’t store the password on the same sheet of paper as the recovery phrase so that, in the event that someone finds the recovery phrase, they still need the password to access the contents of your wallet.
- KeepKey, TREZOR and Ledger Nano S all have the option to set up a passphrase.
Other than to serve as an extra layer of protection, this passphrase can be utilized to create decoy wallets. Any and every entered passphrase “opens” (or, rather, generates) a valid wallet, but only the specific word you entered during the setup will lead you to your actual wallet; therefore, you can create one (or a couple of) decoy wallets that have the same recovery phrase but different passphrases.
If you ever find yourself in a situation where you’re physically forced to reveal the passphrase to your wallet, simply give out the passphrase to one of the decoy wallets. You should, however, prepare for the very worst scenario and assume that your attacker already knows about the concept of decoy wallets. As a response, in order to avoid the 5 dollar wrench attack, you might want to fill up one or two of those decoy wallets with some change so that they seem legitimate when you “give up” the access to them.
Sending and Receiving Crypto
Now that you’ve set up (and understood!) the safety mechanisms of your hardware wallet, let’s look at the way you can use your shiny new device to make transactions.
You can receive crypto on all the accounts that are managed by your hardware wallet by generating a receive address in the wallet’s web application. Luckily, this process has been explained in great enough detail by each vendor so we won’t be covering it in this article.
- Instructions for receiving payments with KeepKey here.
- Instructions for receiving payments with TREZOR here.
- Instructions for receiving payments with Ledger Nano S here.
To make a payment using your hardware wallet, you enter the transaction details into the web applications and then use the hardware device to verify and sign the transaction. Easy peasy.
- Instructions for sending payments with KeepKey here.
- Instructions for sending payments with TREZOR here.
- Instructions for sending payments with Ledger Nano S here.
Specifications
Here are some technical details about each of the three devices that might factor in your decision making process:
| Ledger Nano S | KeepKey | TREZOR | |
| Price | € 79.99 | $ 129.00 | € 69.00 |
| Supported Currencies | Ledger Live (native):
…and 12 more MyEtherWallet:
|
KeepKey Client (native):
|
TREZOR Wallet (native):
MyEtherWallet:
|
| OS Compatibility | Windows
macOS Linux Android ChromeOS |
Windows
macOS Linux |
Windows
macOS Linux Android |
| Width x Height x Depth | 18 mm x 98 mm x 9 mm | 93.5 mm x 38 mm x 12.2 mm | 30 mm x 60 mm x 6 mm |
| Weight | 16.2 g | 54 g | 12 g |
Choosing a Hardware Wallet: Final Thoughts
Hardware wallets are a must for anyone who holds larger amounts of crypto. We truly cannot overemphasize the importance of having a secure, tamper-proof, basically uncompromisable device to store your coins in this day and age when people are getting robbed left and right. While they might be slightly more inconvenient for day-to-day use than other types of cryptocurrency wallets, hardware wallets are amongst the safest of alternatives for the long-term storage of your funds. Each of our three candidates has its strengths and weaknesses; however, they are all quality products that have withstood the test of time so it will be your personal preferences that break the tie.
- The TREZOR is the oldest of the three and the first of its kind, setting the standards for its successors by implementing a device screen. Its plastic case might give it a slightly cheaper feel compared to the alternatives, but its overall design is ergonomically convenient. It is the lightest and most durable of the three, and its screen is slightly bigger than that of the Ledger Nano S. In terms of price, convenience, and security, Andreas Antonopoulos has compared TREZOR to a safe and Ledger Nano to a lockbox.
- The Ledger Nano S is a serious contender since it supports more coins that any of the other options. Another significant advantage is the fact that it supports Ripple (XPR), while TREZOR and KeepKey do not. Its design is reminiscent to that of a regular USB stick, so it’s more likely to go unnoticed than most of the other hardware wallets out there. Its biggest setback would be that it can only hold 5 different cryptocurrency wallets at a time, meaning that every time you want to use your Ledger to transact with a cryptocurrency that isn’t currently on your device, you’ll have to free up space by deleting one of the wallets and then install the one you need. Of course, this doesn’t mean that you’re losing the contents of the deleted wallet; you can just as easily reinstall it on your device the next time you need it.
- The KeepKey definitely takes the cake for its superior design. It has a premium feel to it, and the large screen can fit more information at the same time. However, this otherwise very sleek and modern device is not as inconspicuous as its counterparts, so it may attract some unwanted attention. An interesting feature is that the device only has one button, while TREZOR and the Ledger have two. KeepKey’s biggest limitation is that it doesn’t support as many coins.
Keep in mind that, despite of their differences, all of these hardware wallets are completely viable options for protecting your coins — you can’t go wrong with either one. It all comes down to your budget, your choice of cryptocurrencies and your aesthetic proclivities. In any case, whichever device you choose, please make sure you follow all safety precautions; with all the sophisticated mechanisms hardware wallets have implemented to fight hacking, phishing and malware – the one thing they *can’t* protect you from is yourself!